Patient records turning up in dumpsters, sensitive documents not being shredded and other waste-related “incidents” make headlines, but far greater risk comes from improper disposal of electronic equipment.
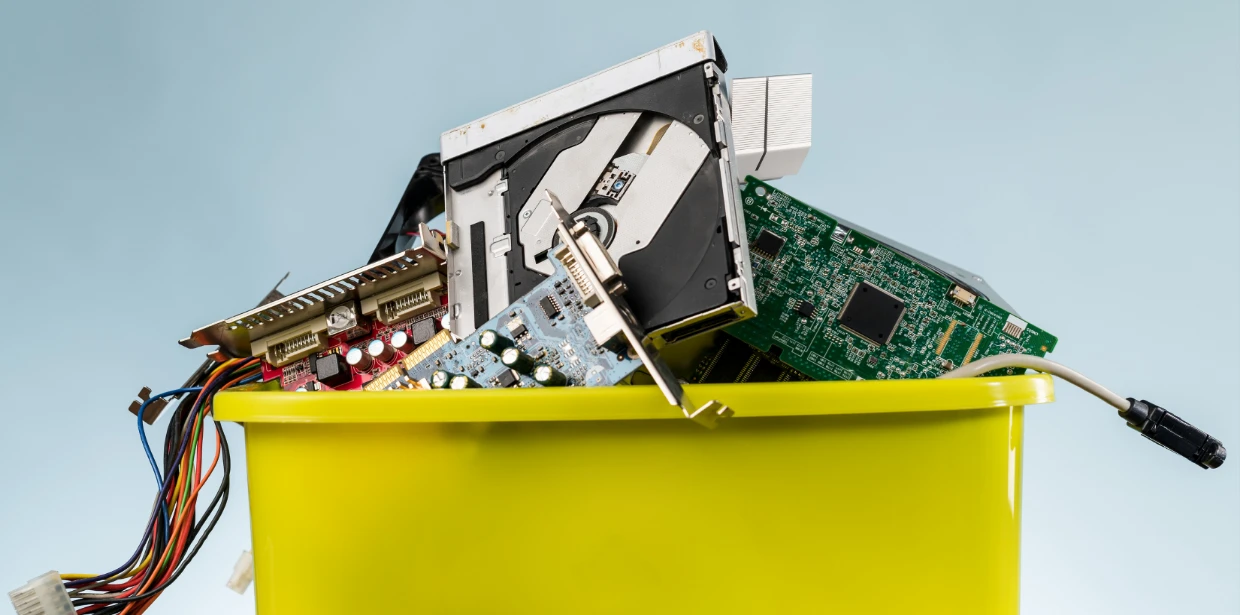
Every year 50 million tons of e- waste is produced as personal and corporate electronics get discarded. This is a huge problem for the planet, as we’ll discuss in a moment, but it is also a problem in terms of data security.
If you dispose of electronic equipment and devices without first deleting the data, you risk being breached by dumpster divers. Last year, anywhere from 5 – 10% (depends on whose stats you use) of corporate breaches were the result of equipment and personal electronics being disposed of improperly.
A whole black-market industry has emerged, consisting of criminals scouring landfills and other sources to obtain USB drives, memory cards, cell phones, laptops, networking equipment and just about anything else that can hold data. These “electronics” are then sold to hackers who have become very adept at stealing personal data and sensitive corporate information. For them it is a gold mine. For you, it’s another potential pitfall.
Why is this “industry” exploding? Often, when corporate equipment is discarded, the data gets deleted, but the hard drives are not properly scoured. There will usually be enough data left behind to do damage.
Cell phones compound the problem. Think about it. We use our phones for everything these days – including accessing company emails, downloading documents and interacting with sensitive material. Some companies don’t bother getting the old phones back when an employee receives an upgrade, so what happens to that phone, and the data it holds, is anyone’s guess.

Even if the employee uses a personal phone for work, few people remember to erase their data before passing the phone on to a friend or family member or worse, throwing it out.
Remove Your Data – or Someone Else May!
Deleting a file is not enough. You can sanitize a device by overwriting the data – and that might be fine for 80% of your equipment. For the remainder, and to be truly safe, requires using a degausser. This is a device that will destroy data on magnetic storage tapes, hard drives, discs, smart phones and other electronic equipment.
Better yet, hire an expert.
There are two ways in which we can help you confidently, securely and confidentially destroy (“disposing of” is not enough!):
- Certified Data Erasure
Specialized encrypted technology is used to sanitize and permanently remove all data from hard drives, mobile devices and other equipment, without damaging the item. The goal is to return the equipment to you so that it can be used by another employee or resold, helping you to maximize the device’s value. - Certified Shred
In this process industrial shredders are used to destroy physical media and electronics. As your devices are turned into metal shards, the process is videoed. Obviously, with this solution there is no usable product at the end, but the pieces can be returned, desired.
Alternatively, you can simply receive the official Certificate of Destruction. This destruction service is compliant with NIST 800-88 Guidelines for Media Sanitization, Department of Defense DoD 5220.22 and Communication Security Establishment Standards CSEC ITSG-06 for Clearing and Declassifying Electronic Data Storage Devices.
You also have the option of allowing the waste to go to a special scrap recovery processor. If you choose this option, you will receive cash for your scrap.
Whether you use our services, or those of somebody else, you should ensure there is a strong Chain-of Custody protocol in place. Our partners have rigourous processes in place to ensure that your data and IT equipment is protected the moment it is picked up your location, through its arrival at our secure facility, and at every step along the way of the recycling or destruction process.

Drowning in an E-Waste Tsunami
Above, we said that 50 million tons of e- waste accumulates annually, and the figure is increasing along with our appetite for our electronics. To put that in perspective, it’s like throwing out 1,000 laptops every second.
The figure bears repeating: 50 million tons – and only 20% gets recycled! It is no wonder the United Nations says we risk drowning under this “e-waste tsunami”.
Protecting the planet is paramount to our collective survival. We can help you do your part. Recycle where you can, by using fake processes described above – or allow the pieces to be used for parts and the balance to be sent to an e-waste scrapping service.
We have chosen Greentec as one of our partners because it has the Certifications to Protect You and the Planet:
- Ontario Environmental Protection Act and Environmental Compliance Approval
- The Personal Information Protection and Electronic Document Act (PIPEDA)
- National Association of Information Destruction Certified (NAID AAA)
- ISO 14001 and SERI R2:2013 Standard Certified

Greentech has also introduced, and continues to follow, all best practices and directions pertaining to COVID-19 safety, provided by our various levels of government.
To learn more about recycling and data cleansing options available, please contact us at [email protected] or (416) 429-0796 or 1.877.238.9944 (Toll Free).
You might also be interested in reading our October 6th post: “Creating Your Breach Response Plan Now Will Save You Thousands Down the Road”.