- News & Resources: Listings >
- Blog
- How OCWA modernized water infrastructure with Cisco industrial IoT
- Redefining physical security in healthcare: A response to rising violence
- Emerging Cyber Threats in 2025: Tactics Redefining Digital Risk
- The Three Shields: How Firewalls Defend Modern Enterprises
- Workplace Safety in Crisis: Protecting Frontline Workers from Rising Threats
- The Role of Industrial Networking in Modern Manufacturing
- Why Cybersecurity for SMBs Must Be a Top Priority in 2025
- Together We Give: CMN and Umbrella’s Commitment to Support our Community
- The State of Shoplifting report reveals that 24% of shoppers switch stores due to shoplifting.
- How to Improve Safety and Security in Schools – Cloud Manage Network
- Top 10 Cybersecurity Threats in 2024
- Microsegmentation: Protecting Data from Cyber Threats
- Retail shoplifting and loss prevention: How to protect your business
- Generative AI Cost Optimization Strategies
- Why Do I Need to Protect My Cloud?
- 10 Reasons for Engaging Outside Experts to Manage Your Cybersecurity
- Why Hiring a 3rd Party MSP Expert Makes Sense and – and Cents (MANY cents!)
- Brand and Network Considerations When Adopting AI Corporately
- Integrating XDR, SIEM, and SOAR
- 3-2-1 –Go? Not so quick, this time.
- 5 Things a CISO Shoud Know
- 10-Step Patch Management Checklist
- Penetration Testing vs. Breach Attack Simulation
- Current big cyber breaches and impact on businesses
- Smart Infrastructure Gets Lit Up!
- Securing Industrial IoT: The Missing Puzzle Piece
- 7 Common Cybersecurity Mistakes Made by SMBs
- The Future of Physical Security: Cloud-Based Systems
- Autonomous and Sensor Technology Use Surging
- 2024 Facilities Trends Will Require Facilities and IT Teams to Work in Tandem
- NGFW vs. WAF. What’s the Right Firewall for You?
- Chris Hadfield’s Words To Live By
- Industrial Revolution 4.0 + IIoT
- Digital Fluency Drives Innovation
- Your Cloud Needs Protecting, Too
- Your building alarm systems could become obsolete. In 2024!
- Zero Trust 2.0: Zero Trust Data Resilience (ZTDR)
- We just got, or got used to, Wi-Fi 6. What is Wi-Fi 7?
- What Does the Board Need to Know? Business Metrics that CISOs Should Share – 4th and Last in a Four-Part Series
- Why 2024 is the Year for AI Networking
- International Women’s Day is Tomorrow – Great Time to Think About…
- Data-Centric Security Step One: Classifying Your Data
- The Network – Unsung Hero of Super Bowl LVIII
- What Does the Board Need to Know? Business Metrics that CISOs Should Share – Third in a Four-Part Series
- Boosting IT Team Performance by Fostering Intuition, Curiosity and Creativity
- Breach Remediation Costs Can Wipeout Bottom Line and Business
- Hoodied Hackers Now Favour Hugo Boss
- What Do You Need to Tell the Board? Business Metrics that CISOs Should Share – Second in a Four-Part Series
- How to Get People to Re-Engage After the Holidays
- What Does the Board Need to Know? Business Metrics that CISOs Should Share – First in a Four-Part Series
- Android Devices MUST be Updated + IT Departments Being Cut as Privilege Escalation Escalates
- Today’s Common Cloud Migration and Management Concerns
- Protect Your Healthcare Network from Cyberattack – Lives are at Stake
- Happy Halloween: Black Cats Lead to Boo….Hoo.
- Insurance Underwriters are Protecting Their Flanks
- Insurance Companies Cracking Down as Cybercriminals Become Better Business Builders
- Scary Cyberattacks Stats
- Parents, Profs and IT Professionals Perceive Back-to-School Through Different Lens
- Zscaler’s new IDTR and other tools that leverage generative AI
- Vanquish Vaping, Vandalism and Villainy
- Fabric for Fast-Paced Environments
- Changes to Cyber Insurance Requirements – What you Need to Know
- Cybersecurity Readiness – Newly Released Report
- Passwords Leaked…Again
- 10-Step Patch Management Checklist
- Remote – Again – For Now… and Still Maintaining Engagement
- Protecting Pocketbooks, Passwords and Property from Pilfering
- Raspberry Robin: Highly Evasive Worm Spreads over External Disks
- Cisco Introduces Responsible AI – Enhancing Technology, Transparency and Customer Trust
- Managing Customer Trust in Uncertain Supply Chain Conditions
- Hope on the Horizon
- Toys of Tomorrow… What will spark your imagination? Fuel your imagination?
- Protecting Purses and Digital Wallets
- The Password that Felled the Kingdom + MFA vs 2FA
- The MOE’s RA 3.0 and Zscaler
- 7 Critical Reasons for MS Office 365 Backup
- Penetration Testing Important, but…
- Social Engineering and Poor Patching Responsible for Over 90% of Cybersecurity Problems
- Breach Incidence and Costs On the Rise Again + 5 Ways to Reduce Your Risk
- Cybersecurity Insurance Policies Require Security Audits and Pen Testing
- Wireless strategies for business continuity gain importance as enterprise expand IoT, cloud, and other technologies
- How Cybercrooks are Targeting YOU
- Enabling Digital Transformation with Cisco SD-WAN
- WFH Post Pandemic – What It Will Look Like. What You’ll Need.
- Leaders to looking to the IoT to improve efficiency and resiliency
- Cyber Security Vernacular – Well, some of it, for now
- Why You Need Disaster Recovery, NOT Just Back-Ups
- 10 Reasons Why Having an Expert Manage Your Cybersecurity Makes Sense and Saves Dollars
- Converting CapEx IT Investments into Manageable OpEx
- The Hybrid Workplace – Planning the Next Phase
- Cisco Cloud Calling: Empowering Customers to Thrive with Hybrid Work
- When You Can’t Access the Cloud
- How to Keep On Keeping On
- New Cisco Research Reveals Collaboration, Cloud and Security are IT’s Top Challenges
- Threats from Within on the Rise
- Cloud Covered? If Not, Take Cover!
- Zero Trust and Forrester Wave Report
- Password Based Cyber Attack: Like Leaving Keys Under Doormats
- So, What’s Up With Sensors?
- Sensors and Systems Create a Digital “Last Mile” and Help Skyrocketing Costs
- Scanners Provide Peace of Mind for Returning Students and Workers
- Sensors Improve Operations and Bottom Line… Easily and Cost-Affordably.
- Cisco Meraki Looks at 2021
- 2020 Holiday Shopping: Cybersecurity and Other Tips to Safeguard Wallets and Systems
- How to make the most of the technology you have
- Personnel, Planet and Business Progress: More Interdependent Than Ever Before
- Sure… you can get them all in the boat – but can you get them to work well together?
- Pushing the Zero Trust Envelope – Cisco is Named a Leader in the 2020 Forrester Zero Trust Wave
- Cloud Data Must be Protected, Too!
- Don’t Let Anyone Get the Dirt on You – Make It Instead!
- How IoT Devices Can Help You and Your business
- WebEx – A World of Possibility
- Creating Your Breach Response Plan Now Will Save You Thousands Down The Road
- Been hacked? Here’s what you must do next.
- The Need for Pen Testing is At an All-Time High
- 5 Ways an IT Reseller Improves Your Performance and Peace-of-Mind
- 5G and Wi-Fi 6: Faster, more flexible, and future ready. Are you?
- Network and Data Security for Returning and Remote Workers + Disaster Recovery Symposium
- Collaboration and Cisco WebEx: Protecting Your Data
- Thursday’s Virtual Conference Tackles Today’s Supply Chain Trials and Tribulations
- 10 Tips to Reduce Cloud Storage Risk
- COVID-19 Crisis Fuelling IT Spending
- Supply Chain/Logistics Experts Share Their Expertise
- Cisco Breach Defence Overview
- Announcing Our New Website and Blog

5 Things a CISO Should Know
by Jane-Michèle Clark, curating Palo Alto's ebook
Aug 06, 2024
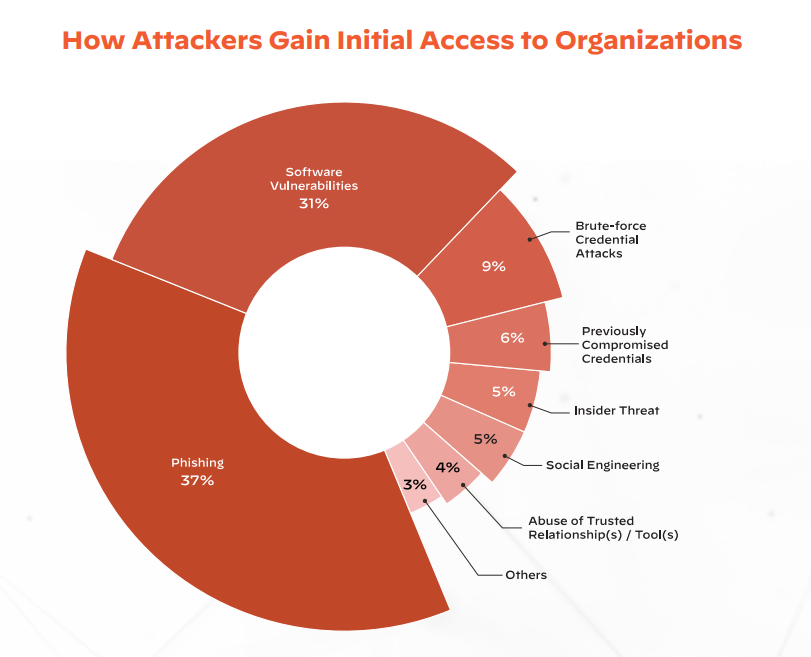
For what seems like forever now, we have been hearing that email is the number one way in which cybercriminals gain access to private networks. The oft-quoted stat is that 99% of threat vectors worm their way in through phishing and social engineering.
We were surprised to learn that phishing, although still #1, but accounts with 37% of successful attacks. The rest:
-
31%: Software vulnerabilities,
-
14%: A combination of insider threats, social engineering and abuse of trusted relationships.
-
9%: Brute-Force Credential Attacks
-
6%: previously compromised credentials that were not changed.
The diagram below, Palo Alto’s Unit 42 Research Shows How Attackers Gain Initial Access to Organisations.
Obviously, things are changing more rapidly than the speed of sound. Just in case anyone is having trouble keeping up, and borrowing heavily from our partner, Palo Alto’s e-book, here are five key topics that CISOs should understand inside and out.
-
Supply Chain Attacks.
With increasingly distributed networks, and hybrid working a fact of life today, organisations are routinely creating virtual spaces in which stakeholders can work collaboratively. All to the delight of cybercriminal enterprises, because once entry is gained into one corporate portal, the marauders can hop, skip and jump their way seamlessly into the networks of other connected organisations.
The result is that multi-stage, multi-vector attacks have become the norm.
Today, it’s also highly possible that one of the stakeholders with whom you collaborate regularly, or one of the firms within your supply chain, manufacturers its products offshore.
One of these companies may do business with a company in Russia, Iran, North Korea or China (the top sources of nation-state threat activities, according to Microsoft’s Digital Defense Report 2022). Now, your network could be vulnerable to a nation-state threat vector. All it takes is the smallest of security shortcomings somewhere along the line, for a massive problem to be unleashed. It’s akin to a small ocean wave encountering interference of some kind and being transformed into a rogue wave, which can be highly destructive.
This has become so problematic that many insurance companies no longer cover nation-state attacks, likening them to acts of war, which are not covered by most policies.
The Solution: Embed Security into the Software Development Pipeline.
MFA can also help, which leads us to number two.
-
Multi Factor Authentication
Thi s is an excellent first line of defence – provided you use it, of course. According to Unit 42 2023 research, “89% of the organizations that fell victim to business email compromise (BEC) attacks had failed to turn on MFA or follow email security best practices. Additionally, in 50% of all Unit 42 incident response cases— BEC or otherwise—organizations lacked MFA on key internet-facing systems such as corporate webmail, virtual private network (VPN) solutions, and other remote access solutions.
The Solution: Integrate MFA for all remote access, internet-accessible, and business email accounts to greatly reduce your organization’s attack surface. To prevent threat actors from circumventing MFA, disable legacy authentications/ protocols and confirm that MFA is not only deployed, but that employees are also using it correctly, and avoid using SMS as a second form of authentication.
-
Cloud Security and Identity and Access Management (IAM)
Improperly configured cloud environments essentially leave the door unlocked for malicious actors, allowing them to gain initial access without needing to find and exploit a vulnerability or make use of sophisticated techniques. It’s no surprise that attackers commonly look for improperly configured cloud environments.
The Solution: Secure Your Cloud Environments with Proper Training and Configuration. Access to cloud controls such as Cloud Services Provider (CSP) consoles, APIs, and command-line interfaces in the cloud should be restricted to only those who need it.
-
Growing Attack Surfaces
Modern attack surfaces are inherently dynamic, and constantly shifting, moving and growing over time. This means that as attack surfaces grow, the number of unmanaged assets across those surfaces grow, too. As a result, attackers are becoming increasingly adept at scanning the internet in search of vulnerable systems and exploiting gaps in security before they can be patched.
The Solution: Conduct an attack surface audit, implement the changes needed, they consider using an attack surface platform (Think: “as a Service”).
-
Overloaded IT teams

