- News & Resources: Listings >
- Blog
- How OCWA modernized water infrastructure with Cisco industrial IoT
- Redefining physical security in healthcare: A response to rising violence
- Emerging Cyber Threats in 2025: Tactics Redefining Digital Risk
- The Three Shields: How Firewalls Defend Modern Enterprises
- Workplace Safety in Crisis: Protecting Frontline Workers from Rising Threats
- The Role of Industrial Networking in Modern Manufacturing
- Why Cybersecurity for SMBs Must Be a Top Priority in 2025
- Together We Give: CMN and Umbrella’s Commitment to Support our Community
- The State of Shoplifting report reveals that 24% of shoppers switch stores due to shoplifting.
- How to Improve Safety and Security in Schools – Cloud Manage Network
- Top 10 Cybersecurity Threats in 2024
- Microsegmentation: Protecting Data from Cyber Threats
- Retail shoplifting and loss prevention: How to protect your business
- Generative AI Cost Optimization Strategies
- Why Do I Need to Protect My Cloud?
- 10 Reasons for Engaging Outside Experts to Manage Your Cybersecurity
- Why Hiring a 3rd Party MSP Expert Makes Sense and – and Cents (MANY cents!)
- Brand and Network Considerations When Adopting AI Corporately
- Integrating XDR, SIEM, and SOAR
- 3-2-1 –Go? Not so quick, this time.
- 5 Things a CISO Shoud Know
- 10-Step Patch Management Checklist
- Penetration Testing vs. Breach Attack Simulation
- Current big cyber breaches and impact on businesses
- Smart Infrastructure Gets Lit Up!
- Securing Industrial IoT: The Missing Puzzle Piece
- 7 Common Cybersecurity Mistakes Made by SMBs
- The Future of Physical Security: Cloud-Based Systems
- Autonomous and Sensor Technology Use Surging
- 2024 Facilities Trends Will Require Facilities and IT Teams to Work in Tandem
- NGFW vs. WAF. What’s the Right Firewall for You?
- Chris Hadfield’s Words To Live By
- Industrial Revolution 4.0 + IIoT
- Digital Fluency Drives Innovation
- Your Cloud Needs Protecting, Too
- Your building alarm systems could become obsolete. In 2024!
- Zero Trust 2.0: Zero Trust Data Resilience (ZTDR)
- We just got, or got used to, Wi-Fi 6. What is Wi-Fi 7?
- What Does the Board Need to Know? Business Metrics that CISOs Should Share – 4th and Last in a Four-Part Series
- Why 2024 is the Year for AI Networking
- International Women’s Day is Tomorrow – Great Time to Think About…
- Data-Centric Security Step One: Classifying Your Data
- The Network – Unsung Hero of Super Bowl LVIII
- What Does the Board Need to Know? Business Metrics that CISOs Should Share – Third in a Four-Part Series
- Boosting IT Team Performance by Fostering Intuition, Curiosity and Creativity
- Breach Remediation Costs Can Wipeout Bottom Line and Business
- Hoodied Hackers Now Favour Hugo Boss
- What Do You Need to Tell the Board? Business Metrics that CISOs Should Share – Second in a Four-Part Series
- How to Get People to Re-Engage After the Holidays
- What Does the Board Need to Know? Business Metrics that CISOs Should Share – First in a Four-Part Series
- Android Devices MUST be Updated + IT Departments Being Cut as Privilege Escalation Escalates
- Today’s Common Cloud Migration and Management Concerns
- Protect Your Healthcare Network from Cyberattack – Lives are at Stake
- Happy Halloween: Black Cats Lead to Boo….Hoo.
- Insurance Underwriters are Protecting Their Flanks
- Insurance Companies Cracking Down as Cybercriminals Become Better Business Builders
- Scary Cyberattacks Stats
- Parents, Profs and IT Professionals Perceive Back-to-School Through Different Lens
- Zscaler’s new IDTR and other tools that leverage generative AI
- Vanquish Vaping, Vandalism and Villainy
- Fabric for Fast-Paced Environments
- Changes to Cyber Insurance Requirements – What you Need to Know
- Cybersecurity Readiness – Newly Released Report
- Passwords Leaked…Again
- 10-Step Patch Management Checklist
- Remote – Again – For Now… and Still Maintaining Engagement
- Protecting Pocketbooks, Passwords and Property from Pilfering
- Raspberry Robin: Highly Evasive Worm Spreads over External Disks
- Cisco Introduces Responsible AI – Enhancing Technology, Transparency and Customer Trust
- Managing Customer Trust in Uncertain Supply Chain Conditions
- Hope on the Horizon
- Toys of Tomorrow… What will spark your imagination? Fuel your imagination?
- Protecting Purses and Digital Wallets
- The Password that Felled the Kingdom + MFA vs 2FA
- The MOE’s RA 3.0 and Zscaler
- 7 Critical Reasons for MS Office 365 Backup
- Penetration Testing Important, but…
- Social Engineering and Poor Patching Responsible for Over 90% of Cybersecurity Problems
- Breach Incidence and Costs On the Rise Again + 5 Ways to Reduce Your Risk
- Cybersecurity Insurance Policies Require Security Audits and Pen Testing
- Wireless strategies for business continuity gain importance as enterprise expand IoT, cloud, and other technologies
- How Cybercrooks are Targeting YOU
- Enabling Digital Transformation with Cisco SD-WAN
- WFH Post Pandemic – What It Will Look Like. What You’ll Need.
- Leaders to looking to the IoT to improve efficiency and resiliency
- Cyber Security Vernacular – Well, some of it, for now
- Why You Need Disaster Recovery, NOT Just Back-Ups
- 10 Reasons Why Having an Expert Manage Your Cybersecurity Makes Sense and Saves Dollars
- Converting CapEx IT Investments into Manageable OpEx
- The Hybrid Workplace – Planning the Next Phase
- Cisco Cloud Calling: Empowering Customers to Thrive with Hybrid Work
- When You Can’t Access the Cloud
- How to Keep On Keeping On
- New Cisco Research Reveals Collaboration, Cloud and Security are IT’s Top Challenges
- Threats from Within on the Rise
- Cloud Covered? If Not, Take Cover!
- Zero Trust and Forrester Wave Report
- Password Based Cyber Attack: Like Leaving Keys Under Doormats
- So, What’s Up With Sensors?
- Sensors and Systems Create a Digital “Last Mile” and Help Skyrocketing Costs
- Scanners Provide Peace of Mind for Returning Students and Workers
- Sensors Improve Operations and Bottom Line… Easily and Cost-Affordably.
- Cisco Meraki Looks at 2021
- 2020 Holiday Shopping: Cybersecurity and Other Tips to Safeguard Wallets and Systems
- How to make the most of the technology you have
- Personnel, Planet and Business Progress: More Interdependent Than Ever Before
- Sure… you can get them all in the boat – but can you get them to work well together?
- Pushing the Zero Trust Envelope – Cisco is Named a Leader in the 2020 Forrester Zero Trust Wave
- Cloud Data Must be Protected, Too!
- Don’t Let Anyone Get the Dirt on You – Make It Instead!
- How IoT Devices Can Help You and Your business
- WebEx – A World of Possibility
- Creating Your Breach Response Plan Now Will Save You Thousands Down The Road
- Been hacked? Here’s what you must do next.
- The Need for Pen Testing is At an All-Time High
- 5 Ways an IT Reseller Improves Your Performance and Peace-of-Mind
- 5G and Wi-Fi 6: Faster, more flexible, and future ready. Are you?
- Network and Data Security for Returning and Remote Workers + Disaster Recovery Symposium
- Collaboration and Cisco WebEx: Protecting Your Data
- Thursday’s Virtual Conference Tackles Today’s Supply Chain Trials and Tribulations
- 10 Tips to Reduce Cloud Storage Risk
- COVID-19 Crisis Fuelling IT Spending
- Supply Chain/Logistics Experts Share Their Expertise
- Cisco Breach Defence Overview
- Announcing Our New Website and Blog

7-minute read, including linked content
As part of our ongoing exploration of the ways in which organisations with distributed operations – and today that is everyone with remote workers, not just multi-branch businesses, municipalities, school boards, healthcare teams and the like – are migrating their businesses to the cloud, and how SD-Wan is an important part of that, we’d like to share two important documents with you:
- An IDC white paper outlining why “SD-WAN technology has been one of the most important advancements for enterprise networks in recent years”. It includes a discussion of the benefits of software-defined WANs, including cost optimization, improved reliability of business applications, and improved productivity levels, among other things. Please click on the link to read “Business Value of Cisco SD-Wan solutions: Studying the Results of Deployed Organisations”.
- Today’s (June 23, 2021) blog post from Cisco. This post is intended for Cisco partners, but the content is beneficial for everyone to read.
Enabling Digital Transformation with Cisco SD-WANBy Stuart Clark |
 |
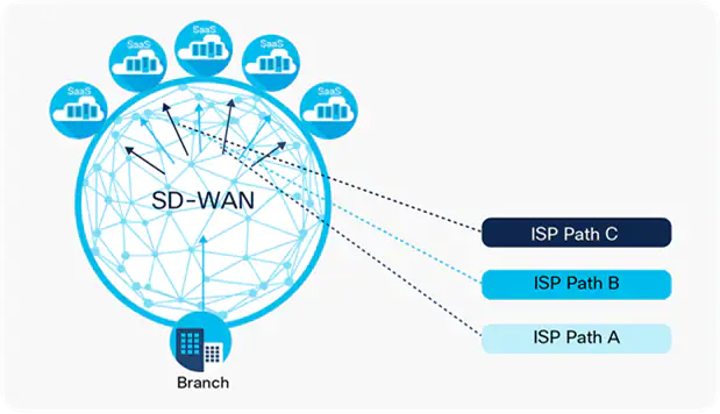
“Cisco SD-WAN unlocks new possibilities with our network infrastructure, the new architecture is replacing the long-established role of the wide-area network (WAN), connecting our users at the branch office location to applications hosted on servers in the datacenters.
Often VPN (Virtual Private Network) tunnels or Multiprotocol Label Switching (MPLS) were implemented for segregation of data and security. This approached worked well for years, but as our customer moved into a mobile digital application world and their data move to the cloud, a new approached was required.
 |
It’s a multi-cloud world
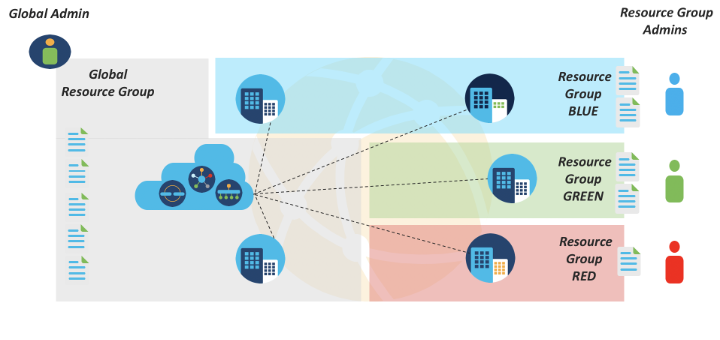
We live in a multi-cloud world, where using multiple clouds from multiple providers has become the new normal. Cisco SD-WAN has proven effective in helping Cisco partners accelerate their adoption of multi-cloud environments and drive business solutions for their customers. It helps them manage multiple network providers, ISP circuits, and connect branches to clouds. Cisco SD-WAN allows customers to deliver on-demand branch connectivity to their ISP and cloud providers directly from the SD-WAN controller. |
Model-Driven Programmability
Adding Cisco SD-WAN programmability via the vManage REST APIs has opened even more possibilities for extending automation to any task. Such as:
- Template-driven infrastructure deployment service, allowing engineers to define building blocks and create abstractions for the deployments of required sets of resources.
- Update or delete the deployed resources with ease without many changes to the configurations.
- Provisions the reference of one resource definition to another, thus enabling the creation of dependencies and controlling the order of creation of resources.
Many Cisco partners are leveraging these APIs to create custom automated sequences for managing, monitoring, configuring, and troubleshooting the SD-WAN environment based on their specific needs.
Getting the details via developer experience
The Cisco SD-WAN API allows Cisco partners to focus more and more on their developer experience. Product managers, marketers, and engineers alike have an interest in evaluating and improving how a developer uses APIs and the benefits they bring. |
|
That’s why Cisco DevNet is dedicated to delivering an excellent developer experience with SD-WAN. It’s a dedication that pays off over many developer interactions, as they use the SD-WAN documentation, sandbox, and other resources.”
To read the post in its original and complete form, please click here.
As companies migrate more of their business applications and data to the cloud, and now that distributed networks are the norm in most industries, it’s critical to look at your cloud and network configurations from a strategic point of view.
We are experts in this area and can help. To learn how, or simply to get more information, please feel free to contact us at i[email protected] or (416) 429-0796 or 1.877.238.9944 (Toll Free).