Superbowl Sunday. A day of super snacks, epic parties, great commercials and a heavily-hyped half-time show. Oh yeah, and a little football with dreams being dashed or realized in the end zones.
Seriously, just as there are heroes on the field, there are plenty of unsung heroes supporting them.
One of these is the network. Not the TV network, but the digital network and WiFi needed to run the event. Without them – even for a few moments – millions of fans would miss out on the Super Bowl part of their celebrations.
To see how CIOs prepare for the big day, please watch the video halfway down the original Extreme Networks’ Superbowl Post.
Also in the video: The NFL’s Deputy CIO, Aaron Amendolia, explains what goes into technology planning and how the network is leveraged to ensure operations, not only on game day but also during the lead-up and days after the Super Bowl:

Cammy Perry, Content Marketing Specialist tells the full story on this Extreme Networks post.
“Every year for the Super Bowl, millions of people across the world tune into the live broadcast while tens of thousands of fans flock to the stadium for the biggest game of the year. What many fans and viewers might not realize is the intricacy of the digital network that ensures a seamless and engaging experience to host this major event.”
For the 11th consecutive season, Extreme Networks served as the Official Wi-Fi Analytics Provider of the Super Bowl, providing the NFL with insights into network performance and how fans engage digitally throughout their experience in the stadium. Through Extreme Analytics, the NFL is able to get insight into how fans engage throughout the game to create an immersive experience.
Setting the Stage for the Biggest Event of the Year
Two years of meticulous planning goes into preparing a host city for the Super Bowl. So, what goes into preparing for the biggest event of the year? It starts with the journey. As fans started heading to Las Vegas for the Super Bowl this year, they were running on Extreme Networks the whole way. From the airports to the roads, the hotels to the casinos, Extreme Networks powers Las Vegas.
Engaging Fans from the Moment They Touch Down in Las Vegas
From the moment fans step off the plane, the goal is to create a seamless and exciting journey. Harry Reid International Airport was most fans’ first and last impression of the city, so the bar for creating an exceptional journey is high. The airport focused on eliminating potential network issues to accommodate the influx of passengers coming through the airport while maintaining safety and smooth operations.
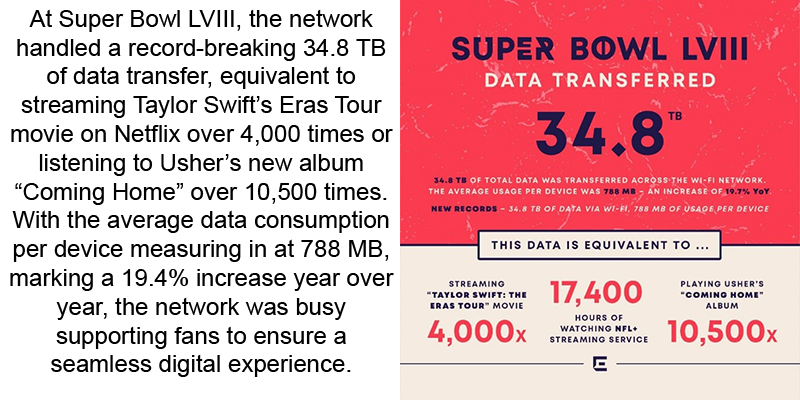
How Did Fans Engage During Super Bowl LVIII?
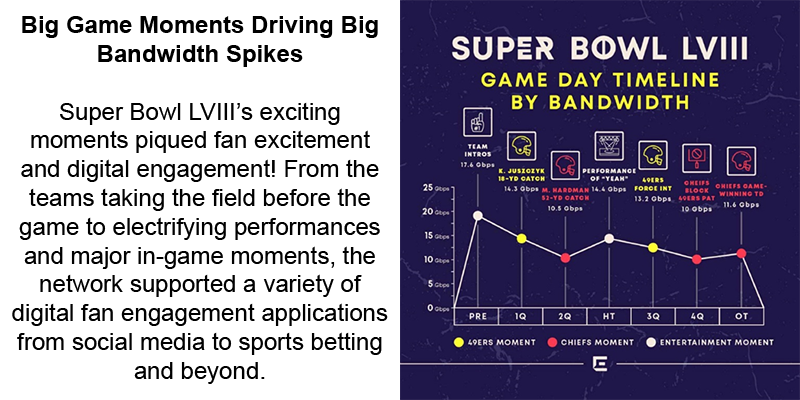
Super Bowl LVIII was filled with thrilling moments that ignited fan excitement and fueled digital engagement. From the pregame ceremonies to big plays, the network supported a range of activities, from social media engagement to sports betting. ExtremeAnalytics provided the NFL with insights into how fans were engaging throughout the game, so real-time adjustments could be made to venue operations, such as opening additional concessions stands and identifying stadium bottlenecks, to provide fans the best possible game day experience.

Not only can we look into the top social media apps during the game, but we can also take that a step further and see what moments drove the most social engagement.
Pre-Game Engagement
During the Pre-Game ceremony, some moments caused big spikes, like the teams taking the field and the coin toss, but ultimately, the moment that drew the most social engagement was Reba McEntire’s singing of the National Anthem. McEntire’s performance created a 1.3 Gbps bandwidth spike on social media apps alone and a 13.2 Gbps bandwidth spike overall.
The First Quarter’s Big Moments
From kick-off through the rest of the first quarter, dozens of exciting plays captured fan interest. While a big 49ers’ play drew the most bandwidth use overall, the top moment for social media came at the end of the quarter when fans were hopeful for a big drive.
Major Plays in the Second Quarter
Going into the second quarter, moments like the 49ers quarterback getting sacked and Taylor Swift being shown on the big screen drew a lot of social engagement, but the big spike of the quarter came during the first touchdown. When the 49ers scored, bandwidth usage on social media spiked to 825.1 Mbps.
Usher’s Halftime Show Performance
The halftime show caused bandwidth spikes throughout its entirety, but two big moments stood out.
- The first major bandwidth spike occurred when Alicia Keys joined Usher on stage to sing their hit songs, “If I Ain’t Got You” and “My Boo.”
- The true biggest bandwidth spike was at the end of the performance when Lil Jon and Ludacris joined Usher to close out the show with the longest-running #1 single of 2004, “Yeah!”
The Second Half Kicks Off
The third quarter was filled with bandwidth spikes from major interceptions to fumbles that impacted the game, but the top moment for social engagement during the third quarter was the Chief’s 57 yard field goal. This field goal made it a 4-point game and created a social media bandwidth spike of 846.7 Mbps.
Fourth Quarter Excitement
With touchdowns, fumbles, sacks, and field goals, the fourth quarter was action-packed. Both teams kicked a field goal in this quarter, and both drew significant social media bandwidth spikes, but what fans captured the most during the fourth quarter was the 49ers’ blocked PAT attempt that left the team only a field goal ahead.
Heading Into Overtime
After a high-scoring fourth quarter, the game was forced into overtime. Social media bandwidth was high from the coin toss to the field goal that gave the 49ers the lead. However, the moment that drew the highest bandwidth usage was the overtime kickoff.
Post-Game Celebrations
After a game-winning touchdown, the red and yellow confetti started falling, and the Kansas City Chiefs players began celebrating. While all that was happening on the field, fans were sharing videos on social media, creating another social media bandwidth spike as they shared videos of Chiefs fans doing the team’s iconic tomahawk chop chant.
The Super Bowl’s Behind the Scenes MVP
While Super Bowl LVIII was filled with all kinds of talent, the true unsung hero emerged not on the field but in the network infrastructure. The network seamlessly supported the fans and stadium operations, making the Super Bowl an immersive digital experience for fans. As the final whistle blew and confetti rained down, the network was there to keep everything connected and running, proving itself to be a behind-the-scenes MVP.”











